The Distracting Sky. #autumn #afternoon #barcelona #raval (via http://instagram.com/p/v3lphToQ76/)

The Distracting Sky. #autumn #afternoon #barcelona #raval (via http://instagram.com/p/v3lphToQ76/)

The Distracting Sky. #autumn #afternoon #barcelona #raval (via http://instagram.com/p/v3lphToQ76/)

“Certainly for artists of all stripes, the unknown, the idea or the form or the tale that has not yet arrived, is what must be found. It is the job of artists to open doors and invite in prophesies, the unknown, the unfamiliar; it’s where their work comes from, although its arrival signals the beginning of the long disciplined process of making it their own. Scientists too, as J. Robert Oppenheimer once remarked, “live always at the ‘edge of mystery’ — the boundary of the unknown.” But they transform the unknown into the known, haul it in like fishermen; artists get you out into that dark sea.”
–Rebecca Solnit,A Field Guide to Getting Lost (viasigned-olivia-tiffany-soga)

The digitization of Charles Darwin’s scientific archive is half completed. When it’s finished, the project will allow researchers and anyone who’s curious to follow the steps that brought the 19th-century naturalist to formulate his evolutionary theory.
“
Now a new analysis of the dial used to predict eclipses, which is set on the back of the mechanism, provides yet another clue to one of history’s most intriguing puzzles. Christián C. Carman, a science historian at the National University of Quilmes in Argentina, and James Evans, a physicist at the University of Puget Sound in Washington, suggest that the calendar of the mysterious device began in 205 B.C., just seven years after Archimedes died. Writing this month in the journal Archive for History of Exact Sciences, Dr. Carman and Dr. Evans took a different tack. Starting with the ways the device’s eclipse patterns fit Babylonian eclipse records, the two scientists used a process of elimination to reach a conclusion that the “epoch date,” or starting point, of the Antikythera Mechanism’s calendar was 50 years to a century earlier than had been generally believed. The finding supports the idea, scientists said, that the mechanism’s eclipse prediction strategy was not based on Greek trigonometry, which did not exist at the time, but on Babylonian arithmetical methods borrowed by the Greeks.
But Archimedes was killed by a Roman soldier in 212 B.C., while the commercial grain ship carrying the mechanism is believed to have sunk sometime between 85 and 60 B.C. The new finding suggests the device may have been old at the time of the shipwreck, but the connection to Archimedes now seems even less likely. An inscription on a small dial used to date the Olympic Games refers to an athletic competition that was held in Rhodes, according to research by Paul Iversen, a Greek scholar at Case Western Reserve University. “If we were all taking bets about where it was made, I think I would bet what most people would bet, in Rhodes,” said Alexander Jones, a specialist in the history of ancient mathematical sciences at New York University. Dr. Evans said he remained cautious about attempting to identify the maker at all. “We know so little about ancient Greek astronomy,” he said. “Only small fragments of work have survived. It’s probably safer not to try to hang it on any one particular famous person.”
Over the years scientists have speculated that the mechanism might have been somehow linked to Archimedes, one of history’s most famous mathematicians and inventors. In 2008, a group of researchers reported that language inscribed on the device suggested it had been manufactured in Corinth or in Syracuse, where Archimedes lived.
–On the Trail of an Ancient Mystery
Solving the Riddles of an Early Astronomical Calculator (viam1k3y)

Château Miranda by schizophonia (via http://flic.kr/p/pUBwjZ )

Château Miranda by schizophonia (via http://flic.kr/p/qc2EUZ )

Château Miranda by schizophonia (via http://flic.kr/p/pUBz7c )

Château Miranda by schizophonia (via http://flic.kr/p/q9KqmW )

Château Miranda by schizophonia (via http://flic.kr/p/pUAkDz )

(via http://flic.kr/p/qasUv9 )

Château Miranda (via http://flic.kr/p/qcz4eT )

L1016123.jpg (via http://flic.kr/p/qasThs )

L1016115.jpg (via http://flic.kr/p/qcz32T )

ゆめからさめない by u-m-e (via http://flic.kr/p/pfLFgc )
Lecture Synopsis: Even though Erno Rubik did not know the mathematics of it, he accidentally designed an object of beautiful symmetry in the Rubik’s Cube. The patterns that appear all over the work of M.C. Escher betray one emotion – symmetry.
You can see it on the Moorish tessellations in…

The Creature from the Red Lagoon via NASA http://ift.tt/1ALafw8

New York City has unveiled a plan to replace its 7,302 pay phones with wireless internet hubs that will offer amenities including free Wi-Fi, free domestic phone calls, USB chargers, and, naturally, advertising space that is projected to generate enough revenue to not only pay for the ambitious project, but also bring the city an additional $500 million in the project’s first 12 years. Dubbed LinkNYC, the network of wireless “Links” is due to be up and running by the end of 2015.
“Today, consumers buy kitchen appliances, and then take them home and do whatever they want with them. But if that product is “connected,” chances are it’s been pre-loaded with someone else’s idea of what a person should be doing with it. And no matter how well meaning that someone else is, when the objects we own contradict us, that’s going to be a frustrating experience.”
–(vianew-aesthetic)
*That was a pretty good analysis from a dozen years ago, and now it explains why “fiction” about cyberpunk is irrelevant. It’s no longer ”aesthetic vision,” it’s everyday lived experience.
Cyberpunk and Empire
Istvan Csicsery-Ronay, Jr.
DePauw University/ Science Fiction Studies
(…)
Nonetheless, I think we can safely identify certain aspects of cyberpunk’s aesthetic vision common to all its examples.
1) “No Future” (the punk in cyberpunk) – the sense of a collapsed future, i.e., the replacement of progressive modernism’s sense of constant material and social improvement by the sense of a failed project, leaving behind ruined infrastructures as its Ozymandian monuments;
2) the replacement of national sovereignty and class consciousness by technically sophisticated, but ethically savage, private, capitalist corporations and cartels, which dissolve social protections and rule of law, while encouraging the ruthless black- marketization of high technologies;
3) the attendant involution of all political power, and with it, the abandonment of all social centrality – hence the tolerance for poverty and decay of social institutions, law, traditional concepts of human dignity, and collective purpose;
4) the street finding its own uses for things – the proliferation of diverse fractal societies and cultures relatively free to construct their own social contracts under the radar of dominant institutions, politically powerless and hence unconstrained by normativity, but potentially destabilizing of the infrastructure of dominance because of their various technical “hacks”;
5) posthuman evolution – the morally unfettered proliferation of technologies (especially cybernetic and biotechnical prostheses) into areas traditionally considered sacrosanct, and, as a result, the gradual transformation of all natural phenomena into artificial ones constructed by human or cybernetic agents.
These might well be considered the characteristics of postmodern Empire. (…)
(via @brucesterling)


20141125 (via http://flic.kr/p/pf9wqQ )

20141124 (via http://flic.kr/p/qc5tvs )

20141122 (via http://flic.kr/p/qc5t4q )

20141121 (via http://flic.kr/p/pfnRTk )

20141120 (via http://flic.kr/p/pUGnKM )

20141119 (via http://flic.kr/p/pUyFWG )

20141118 (via http://flic.kr/p/qbXzk6 )

20141117 (via http://flic.kr/p/qc5qMm )

secrets by andre govia. (via http://flic.kr/p/pRNp9x )
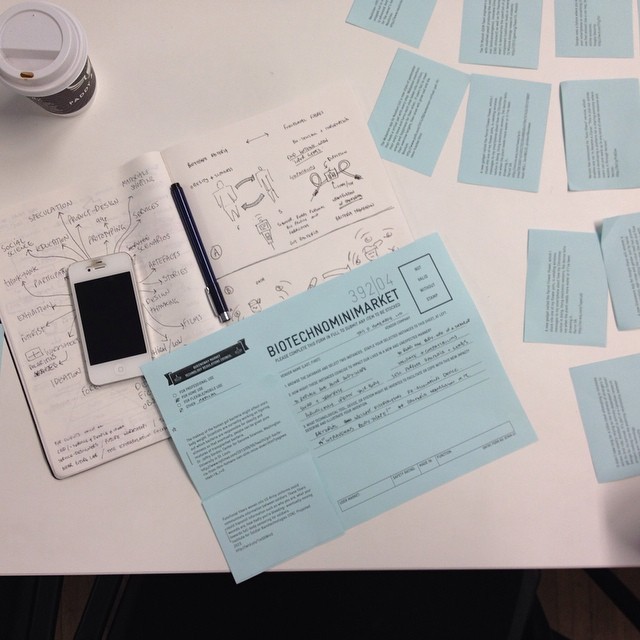
London friends- come to the Design Interactions pop-up opening. BIOTECHNOMINIMARKET Today, 4:30-5:30pm At Queensway Market (via http://instagram.com/p/v0gxEnRrOB/)

Don’t shoot the pianist by Laurent Burnier - www.laurentburnier.com (via http://flic.kr/p/peP6CG )

Hudson by EstherReyes (via http://flic.kr/p/pPScUV )

Untitled by EstherReyes (via http://flic.kr/p/qaib8B )

L1016427.jpg (via http://flic.kr/p/pTZKaU )

L1016423-Edit.jpg (via http://flic.kr/p/qbxSZB )

L1016410.jpg (via http://flic.kr/p/pU7tBz )

L1016405.jpg (via http://flic.kr/p/q9gwdm )

L1016398.jpg (via http://flic.kr/p/qbnCQa )

L1016393.jpg (via http://flic.kr/p/pU7s5X )

L1016388.jpg (via http://flic.kr/p/pTZGBh )

L1016385.jpg (via http://flic.kr/p/q9gutj )

L1016369.jpg (via http://flic.kr/p/qbxQ3K )

L1016361.jpg (via http://flic.kr/p/pU7qta )

L1016354.jpg (via http://flic.kr/p/peyzWq )

L1016348.jpg (via http://flic.kr/p/peMUcg )

L1016313.jpg (via http://flic.kr/p/qbuv8d )

L1016254.jpg (via http://flic.kr/p/peMTr8 )

L1016211.jpg (via http://flic.kr/p/peMT4V )

L1016197.jpg (via http://flic.kr/p/qbxMfR )

L1016196.jpg (via http://flic.kr/p/pTYELJ )

L1016192.jpg (via http://flic.kr/p/pTYEfo )

L1016165.jpg (via http://flic.kr/p/peywto )

L1016154.jpg (via http://flic.kr/p/pU8CqT )

L1016132.jpg (via http://flic.kr/p/pTYCCL )

201411_3-2.jpg (via http://flic.kr/p/qbuqFC )

Hexomniscope Before Anodizing by sneebot (via http://flic.kr/p/5rcp7t )

Readville, Massachusetts by sneebot (via http://flic.kr/p/8beZDM )

Worcester, Massachusetts by sneebot (via http://flic.kr/p/8bmsys )

LoneLady’s ‘Groove It Out’ 12" is out now and available at
http://smarturl.it/grooveitout-itunes
http://smarturl.it/grooveitout-bleep (via http://instagram.com/p/vyoYC5o4wM/)

Agfa Ultra Rapid ( fur Arriflex) by Max Miedinger (via http://flic.kr/p/pXQDFy )

Kelumbayan - Lampung by Hengki Koentjoro (via http://flic.kr/p/qaCcMR )

sports. by jonathancastellino (via http://flic.kr/p/pTwY3i )

[ G ] Jacques de Gheyn (I) - Vanitas Still Life (1621) by Cea. (via http://flic.kr/p/per3Hr )

_9A_0313 by Alksnyte (via http://flic.kr/p/mN1Rts )

|* by dan f.s. (via http://flic.kr/p/dZsLDv )

Shards_1 by mn8er (via http://flic.kr/p/icjjDR )

by ]ezra[ (via http://flic.kr/p/eUYj3W )



WTF by ✠ drakegoodman ✠ (via http://flic.kr/p/9xWxFi )

give me t by _KiRaki (via http://flic.kr/p/oXFiSZ )

Abstract Nature by Mikhail Tormakov (via http://flic.kr/p/pSPgt7 )

dans une lumière essor by Masakazu Chiba|蒔山 (via http://flic.kr/p/qakdx2 )

Soft power by Kaometet (via http://flic.kr/p/q7p6ts )

Piuttosto, mi incuriosiva. by plochingen (via http://flic.kr/p/q9EoWY )
The results show that not all types of spookiness emerge in the same way from the brain. “They show that the neural networks involved in the feeling of a presence are not the same as those involved in out-of-body experiences or in seeing a doppelgänger,” says the lead author of the study, cognitive neuroscientist Olaf Blanke of the Swiss Federal Institute of Technology of Lausanne (EPFL).
http://www.nature.com/news/spooks-generated-by-brain-body-mismatch–1.16294

Ghost Stations of the London Underground

Blue Ice (via http://instagram.com/p/vsc6QlPCC3/)

Nature by Mikhail Tormakov (via http://flic.kr/p/pRQgDk )

Giant disaster immune to policy decisions by brucesflickr (via http://flic.kr/p/q9qvp4 )

Google Maps find of the day (via http://instagram.com/p/vrWFtQKui_/)

20141116 (via http://flic.kr/p/q972Zw )

Tony Dalton related his first hand experiences with a ship’s cat:
“Whilst serving on the Norwegian-flag tanker “Rona Star”, in 1965, I adopted a stray kitten in Mina al Ahmadi which took up residence in the radio room. It refused point blank ever to set foot on shore, despite being bodily carried, many times, down the gangway onto the land. The cat would never leave the ship until the night of June 15th, 1965, when the “Rona Star” was in the wet dock at Rotterdam’s Verolme shipyard, undergoing tank-cleaning. The moggy became extremely agitated, mewling and howling, and left the radio room. I watched it from the cabin window as it scooted down the gangway and disappeared. No sooner had it reached the shore than the ship exploded in a ball of fire and 16 persons were killed. To this day, I swear the damned thing sensed the forthcoming disaster. I never saw it again.”
http://messybeast.com/moggycat/warcat.htm
(via @interdome)


(via Before Abramović, A History of Nothing)
As might be expected, Marina Abramović’s new performance event at the Sean Kelly gallery, Generator, has attracted a healthy level of press coverage that is concomitant with her reputation. Based on a premise of collective sensory deprivation, and the unanticipated insights that this can confer about communication and identity, the Generator experience begins with the voluntary blindfolding of participants and with noise-canceling headphones being placed upon the same. Each gallery-goer attempts to navigate through their environment in this limited state, up until the point where they can raise a hand and be led out of this paradoxically theatrical environment. While this experience will likely be novel to many of her recent converts, the performance has clear precedents among the work of at least one other artist who helped to shape the performance and intermedia subcultures of the mid-late 1970s. Namely, at least two of John Duncan’s events — Maze from 1995 and Voice Contact from 1998–2000 — also involve the voluntary blinding of participants and the subsequent entry of those participants into an unfamiliar space.


Russian Arktika-class nuclear powered Icebreaker Yamal

(via Small Asteroid Impacts Spark Fireballs in Earth’s Sky Every Other Week)

Sometimes I find weird things lying around at @diegorlando’s place… like this teddybear. (via http://instagram.com/p/voSWKmiWkL/)

Week 01: Extrapolation Factory, “Junk Mail Machine” by Storefront for Art and Architecture (via http://flic.kr/p/gTrVM6 )

they.all.fall.down by jonathancastellino (via http://flic.kr/p/q8ie6U )


© David English by leica_camera (via http://flic.kr/p/pQhnhJ )


ANTISCIAN
Collaboration with @jessedraxler and @pouriakhojastehpay /
More at www.someslashthings.com (via http://instagram.com/p/vlr87fkxDT/)

All my dolls and figures in the order of arrival - size and skin color comparison group photo by Hegemony77 doll clothes (via http://flic.kr/p/efUX5j )

Dolls and 1/ 6 scale figures in the order by size - size and skin color comparison group photo by Hegemony77 doll clothes (via http://flic.kr/p/efV3Zd )

Sani Festival, Zanskar valley, India by sandeepachetan.com (via http://flic.kr/p/gs4SCe )

Micro-sections of circuit boards by europeanspaceagency (via http://flic.kr/p/pQ4ozQ )